Are You Ready to Witness the Future of Data Security?
Platform
©2026 QuNu Labs Private Limited, All Rights Reserved.

When the CTO of one of Asia's largest telecom operators publicly confirms the company is engaging global vendors over vulnerabilities surfaced by an advanced AI model, the headline is not the story. The shift underneath it is.
Bharti Airtel's response to Anthropic's Mythos is the first visible signal in Asia of an industry-wide reckoning that European regulators have already legislated against and that has now arrived in the boardroom worldwide.
In April 2026, Anthropic confirmed it was holding Mythos back from general release because the model can identify and potentially exploit serious software weaknesses. Major outlets reported the company was briefing a small set of large tech and financial firms studying it for defensive use. During seven weeks of testing, the model reportedly surfaced around 2,000 previously unknown vulnerabilities. By the week of April 21, the story had shifted again: Anthropic confirmed it was investigating allegations that a small group gained unauthorised access through a third-party vendor.
For two decades, defensive architecture rested on a quiet asymmetry. Vulnerabilities existed faster than attackers could find them. Mythos closes the gap. What used to require months of efforts, now happens in an afternoon, at scale, with a model. The same capability that gives defenders visibility gives adversaries reach.
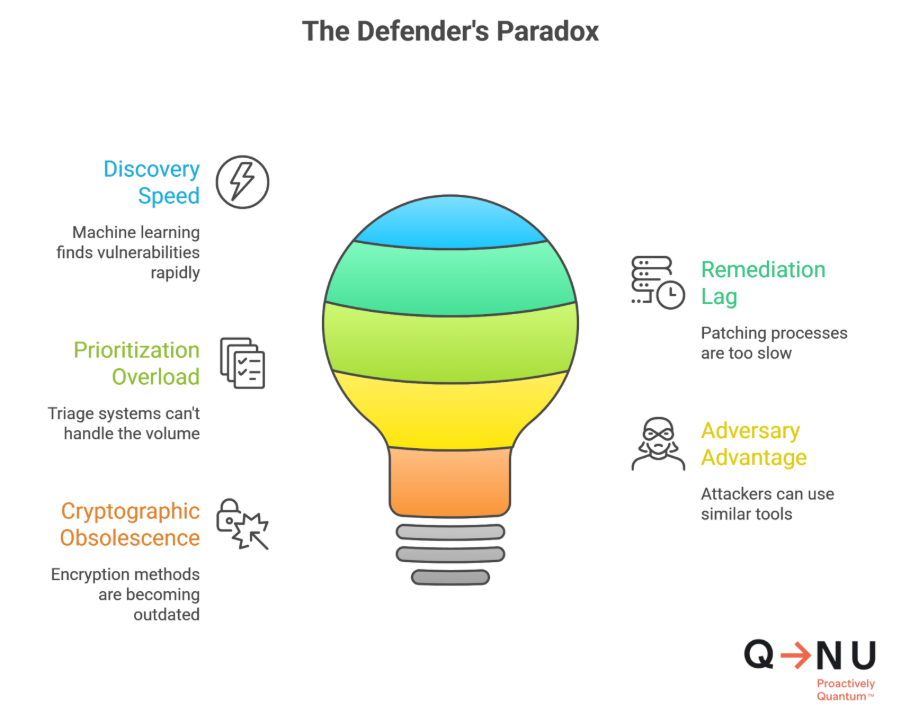
Mythos hands defenders a capability and a problem in the same package.
The capability is real. Vulnerabilities - Including zero-days no human researcher had surfaced now appear at machine speed. A backlog that took a SOC three months to triage can be cleared in a week.
Then the problem starts.
The question every CISO is now being asked privately is whether their environment: In-house systems, vendor APIs, endpoints, identity layers, cloud platforms and OT have the architectural posture to survive an attacker who can find what they couldn't and how will they secure the entire digital ecosystem.
That is what makes Mythos different from previous AI security stories.
The UK and EU put hard civilian-sector deadlines on the table earlier than most of the world. The European Commission's PQC recommendation landed in April 2024, NCSC's phased migration timelines (2028, 2031, 2035) followed in March 2025, and the EU's coordinated 2030 roadmap arrived in June 2025 while most other jurisdictions were still publishing guidance, not deadlines.
The UK's National Cyber Security Centre has published a roadmap guiding critical sectors toward post-quantum cryptography by 2035, with phased planning and migration windows. NCSC's position is direct: PQC, not QKD, is the default migration path for most government and military use cases, and globally connected sectors like finance and telecom should move earlier because they depend on shared protocols and international interoperability.
Two timelines, one direction.
These are not the same threat, and they cannot be addressed with the same tool.
AI accelerates the discovery and exploitation of vulnerabilities sitting on top of the existing system. It is painful and expensive. Organisations breach, recover, harden, and continue.
Quantum is different. A cryptographically relevant quantum computer breaks RSA and ECC, the encryption layer underneath every digital system in the world. Banking transactions, defence communications, identity infrastructure, healthcare records, sovereign data: All of it rests on mathematical assumptions that quantum physics retires. There is no patch and there is no workaround.
And the harvest is already happening. Adversaries are stealing encrypted data today, with no urgency to decrypt it. They are warehousing it for the day a quantum computer arrives. For any data with a shelf life beyond five years, that breach has already occurred and visibility is the only thing missing.
If your migration time plus your data shelf life exceeds the years until quantum capability arrives, you are already too late. The only variable any organisation controls is when they start.
PQC is the default migration path. QKD is a targeted high-assurance tool. Crypto-agility is what makes either of them survivable.
For BFSI, the concern is long-lived confidentiality, payment integrity, identity, and regulatory scrutiny. UK financial-services guidance already treats quantum migration as a strategic planning issue, and the G7 Cyber Expert Group has called for a coordinated PQC roadmap. Most institutions will combine PQC for broad enterprise rollout with selective QKD for very high-value links — inter-bank, treasury, critical data-centre connections.
For telecom, the priority is core networks, signalling, subscriber data, and key management. NCSC has flagged telecom for earlier migration precisely because of its global interoperability constraints. Airtel's response is the first major Asian-carrier signal that the same pressure is now arriving outside Europe.
Automotive flips the timeframe. A car shipped this year may be on the road in 2040, running embedded software whose cryptographic dependencies were chosen before any of this was real. The work here isn't migration, it's designing for migrations you haven't met yet, across V2X, OTA channels, factory systems, and supply chains. Crypto-agility is the architecture.
Aerospace turns the dial up further. Command links and ground-to-satellite traffic carry confidentiality windows measured in decades and operate in contested environments. EuroQCI's space segment exists because no other framework has caught up.
What sits underneath all of these is the same architectural decision. Build crypto-agility into the stack now. Algorithm-swappable libraries, hardware roots of trust, controller-based deployments that push quantum-safe communications across large estates — and the migration becomes survivable as standards finalise. Skip it, and every layer becomes a separate rip-and-replace project later.
What every leader in BFSI, telecom, government and defence, and critical infrastructure should now be discussing internally, is that reactive security has reached its operational limit.
The organisations staying ahead are building quantum-safe architecture before the regulation, the breach, or the headline forces the conversation. They are the ones who treated the quantum problem as an infrastructure deadline, not a research conversation, when the rest of the world was still debating timelines.
QNu Labs has been building for that deadline since 2016. A full stack quantum-safe platform. Sovereign IP, Hybrid PQC and QKD architecture, with QRNG-grade entropy at the foundation. Live deployments across defence, banking, telecom, government, space, and research.
That hybrid architecture answers the question Mythos forces: How do you secure an estate when the attacker's tooling keeps getting smarter? You stop using defences that weaken as quantum compute, AI, and agentic systems advance.
One architecture across every layer: No rip-and-replace, no foreign dependencies, no partial fixes and no dependency on whether the next AI model is friendlier or fiercer than this one.
The Mythos moment is a warning. The harder warning underneath is: Quantum is not a future event. It is a planning constraint already shaping which organisations will still be standing five years from now.
The category is shifting from cybersecurity to cyber-safety. From reactive to proactive and from classical to quantum.
The window is open now, but it is closing sooner than you can imagine.
Start before it's too late. Get your quantum roadmap →
Sources
Mythos coverage and the Airtel response
Regulatory and sector references
No. Anthropic is keeping Mythos out of general release because of its ability to identify and potentially exploit serious software weaknesses and is studying it with a limited set of partners under controlled conditions.
PQC is the default migration path for enterprise-wide rollout because it integrates into existing hardware, software, and cloud stacks. QKD is a targeted tool for ultra-high-assurance links, inter-bank, defence, satellite, select critical-infrastructure backbones. Most regulated organisations will run a hybrid model with crypto-agility underneath both.
NCSC targets UK critical sectors by 2035; the European Commission is pushing member states toward quantum-safe encryption by 2030 via EuroQCI. Beyond Europe, India's MeitY is in talks with Anthropic and the finance minister has convened banks and CERT-In; Singapore's CSA issued an advisory on April 15, and MAS has directed banks to harden defences; South Korea's science ministry is drafting emergency guidelines. Japan, Australia, the UK and US are also engaged.
Inventory every cryptographic dependency across apps, devices, cloud services, and vendor systems. Move to a hybrid classical-plus-quantum-safe deployment during transition. Build crypto-agility in from the start so algorithm swaps do not require re-architecting.