Are You Ready to Witness the Future of Data Security?
Platform
Resources
©2026 QuNu Labs Private Limited, All Rights Reserved.

Your encrypted data is being stolen right now – not to read today, but to decrypt the moment a quantum computer becomes powerful enough. This is Harvest Now, Decrypt Later (HNDL) – the defining cyber threat of 2026, already operational and already targeting governments, banks, hospitals, and defence networks.
Q-Day, when quantum computers crack the RSA and ECC encryption protecting 95% of global digital communications, could arrive within 36 months, as stated in Davos 2026.
Global cybersecurity spend will hit more than $500B this year, yet only 4% of enterprise leaders treat quantum as the most impactful near-term concern. Only 24 of 193 UN nations have quantum strategies (ITU, 2026), a dangerous quantum divide leaving most of the world undefended. The answer is not just better encryption. The answer is 'quantum-safe sovereignty'.
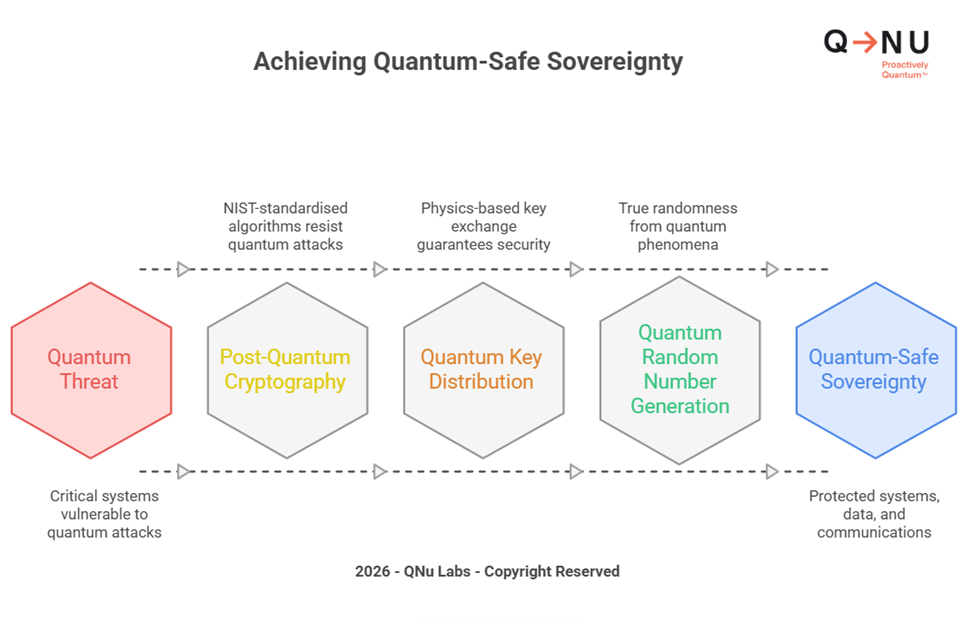
Quantum-safe sovereignty is a nation's or organisation's proven ability to protect its most critical digital systems, data, and communications against quantum threats – using technology it controls, standards it trusts, and infrastructure it owns.
It rests on three pillars:
Adopting another nation's PQC algorithms is better than nothing, but it is not sovereignty. If your keys are generated by foreign hardware or certified only by foreign labs, you have resilience at best and dependency at worst. India's NQM Task Force (Feb 2026) explicitly recommends Tier-3 sovereign-grade PQC labs and indigenous mandates for critical information infrastructure.
The KPMG-projected quantum market reaches $50B by 2030, but the migration window is compressing. NIST finalised PQC standards in August 2024. The US NSA mandates that all new national security systems be quantum-safe by January 2027. The EU requires all member states to begin transition by the end of 2026, with critical systems complete by 2030. BCG has warned, "Starting in 2030 will already be too late." The average classical breach costs $4.44M. A quantum-enabled retroactive decryption of a decade of financial settlements or government intelligence? Incalculable. Irreversible.
Nation-states are archiving military communications today. Key applications: quantum-secure command and control, QKD-protected satellite uplinks, free-space QKD for mobile units, and quantum-safe drone communications. India's Army, Navy, and defence training institutions are already protected.

5G core signalling, SIM authentication, and roaming protocols all rely on RSA and ECC. The GSMA Post-Quantum Telco Taskforce has formally warned of quantum exposure.
Applications: QKD on fibre backbone, quantum-safe TLS for 5G core, QRNG-based network entropy, and QConnect / QVPN for secure government channels.
HSBC ran the world's first quantum-safe bank trade — a simulated €30M FX deal using QKD+PQC. JPMorgan's Q-CAN runs live in Singapore over existing fibre.
Applications: quantum-safe SWIFT, PQC-signed digital transactions, QKD for data-centre interconnect, and QRNG for OTP and transaction signing.
Patient records and genomic data carry a 50–100-year shelf life. The US FDA has signalled that devices approved in the late 2020s must include crypto-agility.
Applications: PQC-secured EHR systems, quantum-safe telemedicine, and QKD for national health ministry data exchange.
Power grids, railways, and airports run on OT hardware with 20–30-year lifecycles designed before quantum was a threat.
Applications: QKD-secured SCADA networks, PQC-authenticated remote OT access, and quantum-safe satellite telemetry for pipelines. India's RailTel is an active deployment partner.
Connected vehicles create millions of attack surfaces, each outliving today's encryption.
Applications: quantum-safe V2X protocols, PQC for OTA firmware signing to prevent spoofed malicious updates, QRNG for in-vehicle HSM key generation, and quantum-safe EV charging authentication. Siemens, Honeywell, and Rockwell Automation are beginning OT quantum-safe transitions.
Applications: quantum-safe national ID and biometric authentication, PQC-secured inter-ministry communications, QKD for diplomatic channels, and post-quantum secure government cloud. Explore QNu's QShield platform for enterprise-wide governance.
Here is a quick list of the forward-looking nations on their quantum security journey:
Also, understand various threat vectors, global regulations and their implications; hence, what each industry and organisation should be doing in our “Industry-Based Threat Intelligence Reports” and “PQC Migration Playbook for CXOs”.
Building a sovereign quantum-safe architecture needs four interlocked layers:

India's quantum security advantage is not theoretical. It is certified, deployed and operational — making India one of the few nations globally with proven quantum-safe infrastructure in active use.
Suggested Read:
Get to know Quantum Readiness in Cybersecurity Report 2025–26 and explore the complete QShield platform.
Quantum-safe by design is the new secure by design. Organisations that act in 2026 will set the standard. Those who wait will comply at a crisis premium. Sovereignty in encryption is sovereignty in everything — from banking to the battlefield. Every sector has a different clock. But the harvest is happening now, across every sector, at every border.
Start with a cryptographic inventory. Build towards the four layers. Demand indigenous certification.
The QShield platform is your one-stop solution for PQC governance across your entire organisation.
Explore QNu's Quantum Readiness Report 2025–26 or reach the team at qnulabs.com.
Sources & External References
Quantum-safe sovereignty refers to the ability of a nation or organisation to secure its digital infrastructure against future quantum threats using trusted technologies, controlled standards, and verifiable systems. It combines post-quantum cryptography, quantum key distribution, and quantum-based randomness with strong governance and certification frameworks.
The urgency stems from the growing risk of data being intercepted today and decrypted later when quantum capabilities mature. Sensitive information—especially in defence, banking, telecom, and healthcare—has long-term value, making an early transition to quantum-safe systems a strategic necessity rather than a technical upgrade.
It describes a strategy where attackers collect encrypted data now and store it until quantum computers can break current encryption methods. This creates a delayed but inevitable breach risk, particularly for high-value data with long lifecycles.
Q-Day is the point at which quantum computers become capable of breaking widely used encryption methods such as RSA and ECC. Once this threshold is crossed, many existing security systems could become ineffective unless already upgraded.
Post-quantum cryptography (PQC) replaces vulnerable algorithms with quantum-resistant ones and can be deployed across existing systems. Quantum key distribution (QKD), on the other hand, uses principles of physics to securely exchange encryption keys, making it suitable for highly sensitive communication channels. Both approaches complement each other in a layered security model.
Quantum random number generation produces true randomness derived from quantum processes. This enhances the strength of encryption keys and improves the integrity of secure communications, authentication systems, and cryptographic operations.
Sectors handling critical or long-life data face the highest exposure. These include defence, financial services, telecom networks, healthcare systems, government infrastructure, and industrial control environments. Early adoption in these sectors is essential to reduce systemic risk.
The starting point is identifying where current cryptographic systems are used across applications, networks, and devices. From there, organisations should prioritise high-risk areas, adopt crypto-agile architectures, and gradually integrate quantum-safe technologies.
While PQC is essential, it is only one part of a broader strategy. High-assurance environments often require additional layers such as secure key distribution, trusted hardware, and sovereign validation frameworks to achieve complete resilience.
India has taken meaningful steps through national initiatives, infrastructure deployments, and policy frameworks aimed at strengthening quantum readiness. Efforts include secure communication networks, defence applications, and structured roadmaps under national programmes focused on quantum technologies.