Are You Ready to Witness the Future of Data Security?
Platform
©2026 QuNu Labs Private Limited, All Rights Reserved.

The G7 has set the timetable. The data is already being collected. The window to act is shorter than most banks realise.
Something shifted in global banking this year. In January 2026, the G7 Cyber Expert Group, co-chaired by the US Treasury and the Bank of England, set the timetable: critical financial systems migrated to post-quantum cryptography by 2030–2032, full migration complete by 2035. [1] While most banks are still planning, QNu Labs has already delivered. A top European multinational bank, founded in the 1800s, operating across 50+ countries, holding €1.48 trillion in total assets, and designated a systemically important financial institution by the Financial Stability Board partnered with QNu to migrate critical infrastructure to a quantum-safe architecture which is NIST-aligned & ANSSI-compliant.
India's banking sector is now on that same clock. The Finance Ministry has directed public sector banks to investigate quantum-resistant encryption. Punjab National Bank, with IIT Kanpur, launched PSB Hackathon 2026 with the theme "Quantum-Proof Systems for Public-Facing Applications." [2] The RBI has been in active conversations with the US Federal Reserve and the Bank of England on the quantum threat to financial systems.
When three of the most powerful financial regulators on the planet are in the same room discussing a single threat, the threat is real, it is close, and it is time to move.
The public conversation around quantum risk tends to focus on Q-Day. That future moment when a quantum computer finally becomes powerful enough to crack encryption. That framing creates a dangerous illusion. That the problem starts then. But it does not.
The threat that is active right now is called Harvest Now, Decrypt Later (HNDL). Nation-state adversaries and sophisticated threat actors are intercepting encrypted data today. Banking records. SWIFT communications, Customer KYC files: All being stored with the specific intention of decrypting it once quantum computers are powerful enough. The US Department of Homeland Security, the UK's National Cyber Security Centre, the EU Agency for Cybersecurity, and the Australian Cyber Security Centre all base their post-quantum guidance on the premise that this collection is already happening. [3]
There is no alarm when HNDL occurs. No breach notification or no anomaly in your logs. The encryption holds for now. But the data has already left your perimeter.
Sensitive communications captured in 2026 could be decrypted in 2032. [4] The breach does not happen when data is stolen. It happens years later, when the encryption protecting it collapses. For a bank holding loan records, credit histories, and KYC data with a fifteen to twenty year sensitivity window, that timeline is not comfortable.
Every cross-border SWIFT message, every interbank settlement, every digital signature, every OTP, every dollar-clearing leg of a correspondent banking relationship rests on classical cryptographic algorithms: RSA, ECC & Diffie-Hellman. These were built for a world without quantum computing. That world is changing faster than most institutions have accounted for.
In 2019, breaking RSA-2048 encryption was estimated to require 20 million quantum qubits. A scale so distant it felt theoretical. In May 2025, Google Quantum AI researcher Craig Gidney published research showing it could be done with fewer than one million qubits in under a week. [5] By February 2026, researchers at Iceberg Quantum proposed an architecture that could bring that number below 100,000. [6]
Three papers in thirteen months drove a 200-fold reduction in the estimated resources needed to break RSA-2048. What experts once placed in the 2040s is now being discussed for the early 2030s.
Mastercard has published global migration cost estimates of $28 to $42 billion across the financial sector. [7] India's National Quantum Mission, backed by a Rs. 6,003.65 crore government outlay explicitly identifies protecting banking and financial systems as a strategic national priority. [8]
The encryption assumption your bank is built on is being dismantled in research labs right now. The question is whether you will be ready when it gives way.
Nearly 80% of the world's 50 largest banks are now actively engaged with quantum technology, shifting from experimentation to strategic investment. [9] JPMorgan, HSBC, Goldman Sachs, Barclays, BNP Paribas, BBVA, Intesa Sanpaolo, Standard Chartered, ANZ, Commonwealth Bank, and UOB are all running active quantum pilots. QNu Labs sits inside this peer group, and our European deployment is one of the few production-grade quantum-safe cryptographic frameworks running today inside a Tier-1 systemically important bank.
Large private Indian banks are running pilots in post-quantum cryptography and testing hybrid encryption systems. Public sector banks are moving more slowly, preparing for large-scale cryptographic audits across legacy infrastructure. [10]
The legacy problem is not trivial, globally or domestically. Identifying every cryptographic instance across apps, ATMs, APIs, data centres, and cloud environments is, as one technical analysis puts it, "archaeological-level work." [11] The encryption is not in one place. It is in every system, every vendor integration, every network layer.
The regulatory map is now synchronised. NSA CNSA 2.0 mandates PQC for US national security systems by 2030, with full migration by 2035. EU DORA requires ICT risk management explicitly inclusive of quantum threats. The Monetary Authority of Singapore has mandated cryptographic inventories by 2025 and full PQC adoption by 2030. India's NQM task force recommends most organisations begin structured preparation by 2028, with full adoption targeted by the early 2030s. [12]
The institutions that begin now will be ahead of those mandates. The ones that wait will be scrambling to meet them under correspondent banking pressure.
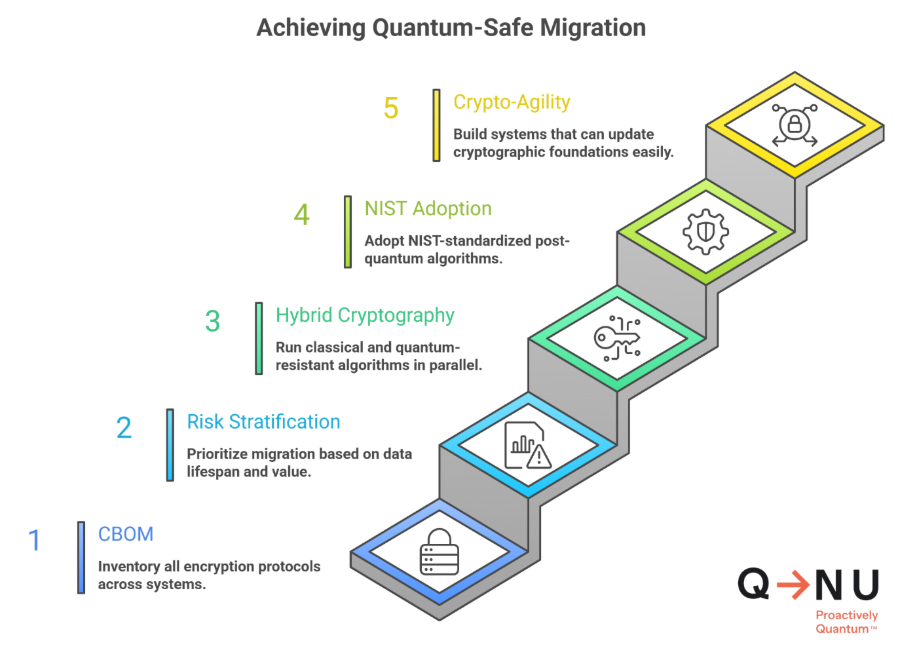
Quantum-safe migration is not a software update. It is a phased, multi-year process aligned to the same five-stage roadmap published by the G7 CEG, the World Economic Forum, and Mastercard.
A full inventory of every encryption protocol across every system. The exact deliverable PSB Hackathon 2026 is building tooling for, and the foundational baseline of MAS, ENISA, and UK NCSC migration mandates.
Prioritise migration based on data lifespan and strategic value. Customer data held for twenty years carries a fundamentally different risk profile than a ninety-day transaction log.
Run classical and quantum-resistant algorithms in parallel during the transition. This ensures backward compatibility while progressively hardening the cryptographic foundation.
NIST finalised its first post-quantum standards in August 2024: FIPS 203, FIPS 204, and FIPS 205. Regulators in the UK, Canada, Germany, Australia, and Singapore have aligned national guidance to these. [13]
Build systems that can update their cryptographic foundations without a full overhaul. The standards will continue to evolve. Your architecture must be able to keep pace.
Previous cryptographic migrations at institutional scale have taken five to ten years. The G7 CEG identifies 2030 to 2032 as the critical window. The urgency is self-evident.
There is a temptation to treat this as a future budget item. That temptation is exactly what HNDL exploits.
Every day without a cryptographic inventory is another day of exposure accumulating in someone else's storage. Every procurement cycle that does not include quantum-readiness requirements is infrastructure that will need replacing under pressure rather than on a planned timeline. Every year of delay is a year added to the migration window on the wrong end.
India processed 22.64 billion UPI transactions in a single month. That scale is a source of national pride. It is also a surface area. Every cross-border leg of that volume runs onto global rails operated by counterparties already migrating to quantum-safe standards. Lag the curve and you become the weak link. [14]
QNu Labs is the global category leader in QKD by MarketsandMarkets and the only full-stack quantum security company building from India for the world. Our European deployment is the proof of how. Three live use cases — cryptography, secure communications, and authentication — delivered through QRNG plus PQC integration for authentication certificates, QVPN double-layered tunnelling for PQC-encrypted traffic, and a flexible QRNG rental model that absorbed quantum-grade entropy into the bank's existing infrastructure. Plug-and-play deployment. Zero disruption to retail or wholesale banking flows. NIST FIPS 203/204/205 compliant. ANSSI-aligned. Sovereign by design.
The cryptographic inventory tools, hybrid deployment frameworks, and NIST-aligned algorithms your institution needs are not theoretical. They are in production today, deployed inside one of Europe's most regulated financial institutions.
The only variable is when your institution decides to start.
Assess your quantum readiness →
[2] PSB Hackathon 2026, Punjab National Bank / DFS, Ministry of Finance, Feb 2026
[3] Harvest Now, Decrypt Later: The Quantum Threat is Already Here, Freshfields, Dec 2025
[4] Harvest Now, Decrypt Later: What Leaders Do Now, SafeLogic, Mar 2026
[5] Google Researcher Lowers Quantum Bar to Crack RSA Encryption, The Quantum Insider, May 2025
[7] Preparing for a Post-Quantum World, Mastercard White Paper, Oct 2025
[8] National Quantum Mission, Press Information Bureau, Government of India
[9] Global Banks Embrace Quantum Technology Race, TechInformed / Evident Research, Mar 2025
[10] Quantum-Safe Encryption: Is Indian Banking Prepared for 2030?, Billcut
[11] Post-Quantum Cryptography: India's Migration Strategy, Medium / Sankalp Joe, Nov 2025
[12] India Reveals National Plan for Quantum-Safe Security, The Quantum Insider, Feb 2026
[13] NIST Post-Quantum Cryptography Standards, August 2024
[14] UPI Records 22.64 Billion Transactions in March 2026, The Tribune / ANI, Apr 2026
Quantum-safe encryption uses algorithms resistant to quantum attacks. Banks need it because quantum computers will break RSA and ECC, the cryptography protecting every transaction and customer record. Migration takes five to ten years. The G7 has set a 2030–2032 deadline for critical systems. Waiting until Q-Day arrives guarantees exposure across every cross-border settlement chain.
The G7 Cyber Expert Group has set 2030–2032 for critical financial systems and 2035 for full migration. NSA CNSA 2.0 mandates PQC by 2030. EU DORA requires it under operational resilience. MAS Singapore mandates cryptographic inventories by 2025 and adoption by 2030. India's National Quantum Mission targets the early 2030s.
Because the breach does not start when quantum arrives. Data is already being collected today under “Harvest now, Decrypt later. By the time quantum systems can decrypt it, the exposure is already locked in.
Start with a Cryptographic Bill of Materials — a full inventory of every encryption protocol across every system. Without it, you cannot prioritise what to migrate. PSB Hackathon 2026 is building tooling for exactly this. MAS, ENISA, and the G7 CEG have all anchored their roadmaps on the same starting artefact.